Introduction
With this post, we continue our investigation on the best solutions for communication that, in our opinion, are valid alternatives to the most known and popular ones, but that we believe have characteristics that allow, especially to the user, to have full control over their personal data.
It is not our intent to create comparisons between the solutions we describe because we believe that it is not correct and that the user chooses the resource he prefers.
What is XMPP?
XMPP is a protocol and precisely “XMPP is the Extensible Messaging and Presence Protocol, a set of open technologies for instant messaging, presence, multi-party chat, voice and video calls, collaboration, lightweight middleware, content syndication, and generalized routing of XML data.” (this is the definition we find on the official website of XMPP).
The XMPP protocol was formalized in 2004 by the IETF (The Internet Engineering Task Force) under the name “Extensible Messaging and Presence Protocol (XMPP)”.
Always on the official site, more specifically in the FAQ section, we read
“XMPP is a powerful, open, secure, standards-based protocol. It is a freely-available technology for real-time communication, which powers a wide range of applications including instant messaging, presence, collaboration, voice and video calling, Internet of Things, tactical military messaging, mobile cloud push, and more.”.
Therefore, it’s possible to use this protocol for real-time communication, enhanced by a wide range of applications including those of messaging, presence, collaboration, voice and video calls, Internet of Things, military tactical messaging, mobile cloud push and others.
In essence, it’s a powerful protocol that allows for numerous applications.
As explained in the FAQ, the XMPP protocol is undoubtedly used for instant messaging based on a federated chat network composed of thousands of servers.
However, always in the FAQ, it is further specified that the XMPP protocol is also usable for machine-to-machine (M2M) signaling systems, both in the presence and in the absence of a federation. With the XMPP protocol, one can develop and manage IoT systems for remote control of any object or device.
This brief description of the XMPP protocol leaves no doubt about its potential in the application field.
There is no doubt that the most widespread applications of the XMPP protocol are those related to instant messaging, so much so that it - which dates back to 1999 - has been used by several large companies and continues to be still today the basis for several projects.
The XMPP site at the section software-server provides information about some projects, among which we mention Prosody IM.
The characteristics of the XMPP protocol
Before continuing with our in-depth study, we consider it worthwhile to indicate the characteristics of the XMPP protocol as officially declared on the XMPP site in the section “Overview”.
There is no doubt that these are definitely striking aspects, retrieved from the official website, and listed below:
Open — the XMPP protocols are free, open, public, and easily understandable; in addition, multiple implementations exist in the form of clients, servers, server components, and code libraries.
Standard — the Internet Engineering Task Force (IETF) has formalized the core XML streaming protocols as an approved instant messaging and presence technology. The XMPP specifications were published as RFC 3920 and RFC 3921 in 2004, and the XMPP Standards Foundation continues to publish many XMPP Extension Protocols. In 2011 the core RFCs were revised, resulting in the most up-to-date specifications (RFC 6120, RFC 6121, and RFC 7622).
Proven — the first Jabber/XMPP technologies were developed by Jeremie Miller in 1998 and are now quite stable; hundreds of developers are working on these technologies, there are tens of thousands of XMPP servers running on the Internet today, and millions of people use XMPP for instant messaging through public services such as Google Talk and XMPP deployments at organizations worldwide.
Decentralized — the architecture of the XMPP network is similar to email; as a result, anyone can run their own XMPP server, enabling individuals and organizations to take control of their communications experience.
Secure — any XMPP server may be isolated from the public network (e.g., on a company intranet) and robust security using SASL and TLS has been built into the core XMPP specifications. In addition, the XMPP developer community is actively working on end-to-end encryption to raise the security bar even further.
Extensible — using the power of XML, anyone can build custom functionality on top of the core protocols; to maintain interoperability, common extensions are published in the XEP series, but such publication is not required and organizations can maintain their own private extensions if so desired.
Flexible — XMPP applications beyond IM include network management, content syndication, collaboration tools, file sharing, gaming, remote systems monitoring, web services, lightweight middleware, cloud computing, and much more.
Diverse — a wide range of companies and open-source projects use XMPP to build and deploy real-time applications and services; you will never get “locked in” when you use XMPP technologies.
We do not intend to move our intervention to a very technical level, but anyone interested can read the documentation available on the XMPP website.
There is no doubt that to appreciate the XMPP protocol better, it would be advisable to have even minimal computer knowledge to understand its architecture, development, and other dynamics.
However, we will try to unravel the main doubts in the continuation of this article.
The protocol core
Although these are very technical aspects, we believe it is appropriate to highlight what the characteristics of the XMPP core are, also in terms of security.
The core of the protocol, as we read on the official website, is:
- The base XML streaming layer
- Channel encryption using Transport Layer Security (TLS)
- Strong authentication** using the Simple Authentication and Security Layer (SASL)
- Use of UTF-8 for complete Unicode support, including fully internationalized addresses
- Built-in information about network availability ("presence")
- Presence subscriptions for two-way authorization
- Presence-enabled** contact lists (“rosters”)
Who is behind XMPP?
Everything is made clear on the XMPP website, as we read the following:
“The XMPP Standards Foundation (also known as the XSF and formerly the Jabber Software Foundation) is an independent, nonprofit standards development organisation whose primary mission is to define open protocols for presence, instant messaging, and real-time communication and collaboration on top of the IETF’s Extensible Messaging and Presence Protocol (XMPP).”
The XSF role is highly relevant to clear the field of possible doubts on the possible presence of “business” subjects that, in some way, can condition decisions.
XSF is a guarantee that an independent and non-profit entity oversees the processes related to the XMPP protocol.
Messaging Security: The OMEMO Protocol
An essential aspect of message exchange is to ensure that adequate security conditions are in place to minimize risks.
The OMEMO Multy-End Message and Object Encryption protocol is an XMPP extension for secure multi-client end-to-end encryption.
OMEMO It is an open standard based on a Double Ratchet and PEP that anyone can use and implement freely.
Moreover, the protocol has been audited by a third party.
On this page, you can see a small table comparing the characteristics of OMEMO with other protocols.
Also, on this page, you can track the progress of OMEMO integration in XMPP clients (applications).
What is the concrete use for the user?
So far, we have had to expose some aspects, probably very technical, but it was necessary to put them before the more practical part of this contribution.
The question we expect from the reader is: “What are the concrete uses of the XMPP protocol for the user?”.
On the XMPP website, there is the section “Uses” in which you can consult the projects for each of the individual categories indicated and precisely :
- Instant Messaging;
- Internet of Things;
- Online Gaming;
- Social;
- WebRTC.
However, XMPP is probably best known for instant messaging systems, so that we will refer to these according to our experience with Apple systems.
First step: have an XMPP account
The first thing to consider is using an instant messaging system with XMPP; you need an account similar to an email address like user@dominio.com.
Small notation: some XMPP servers have the domain extension .im to indicate that it is an instant messaging system.
There are several ways to create and use an XMPP account.
- I can get the XMPP account from an existing XMPP provider (you can see it on the official XMPP site here: https://list.jabber.at).
- Alternatively, we can decide to install an open-source XMPP resource on a server and use it on our own.
In our case, we opted for both solutions: we obtained an account with an existing XMPP provider and installed an XMPP service on our server, which is Snikket. Regarding Snikket, we refer to our previously published contribution.
Among the existing XMPP providers, we tried Tigase and Disroot. You can also activate an account via the Beagle app, which we indicate below by selecting Preferences->Account->Add.
Which apps to use?
In this paragraph, we’ll describe some apps we’ve tried on MacOS and iOS systems.
For MacOS
On macOS systems, the best app, in our experience, is Beagle, which is available on the App Store.
Here are some pictures of the app on the App Store
The chat window looks like the following
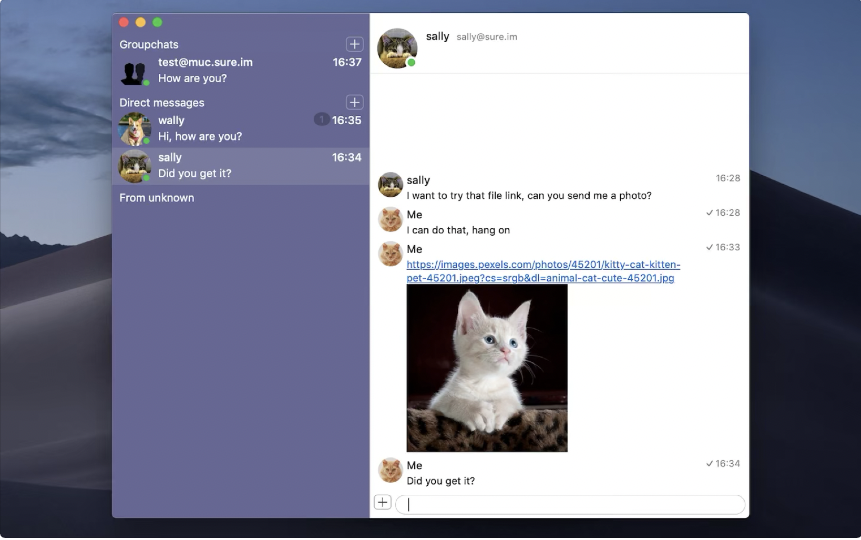
We can consult our contacts as in the following image

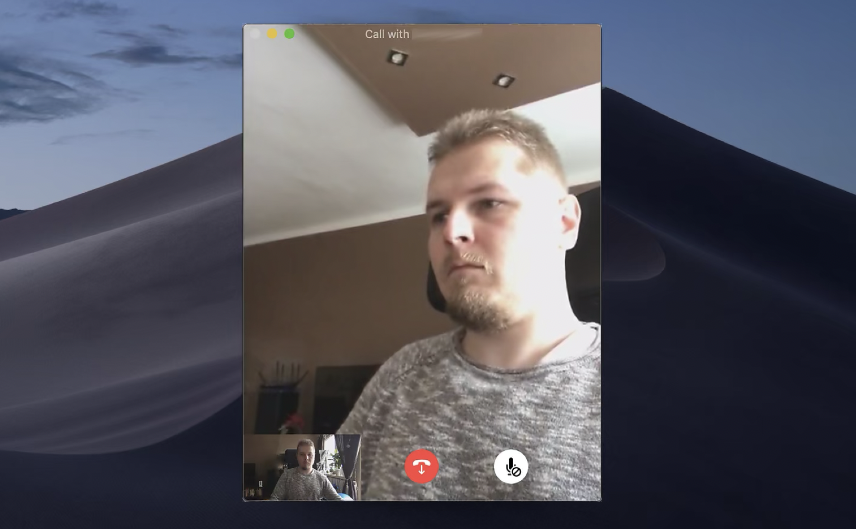
Since we said that with the XMPP protocol, calls and video calls are also possible, here is an image of a video call
Regarding the preferences, you can manage the general settings
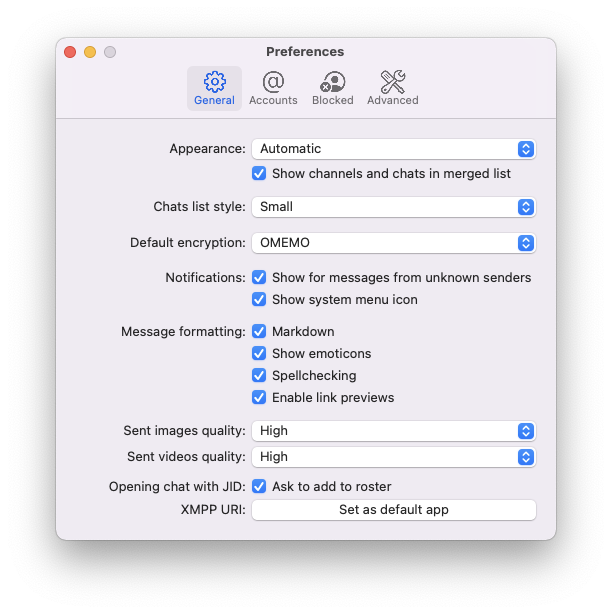
You can see from the image that you can choose OMEMO for the default encryption.
Then there are the account preferences
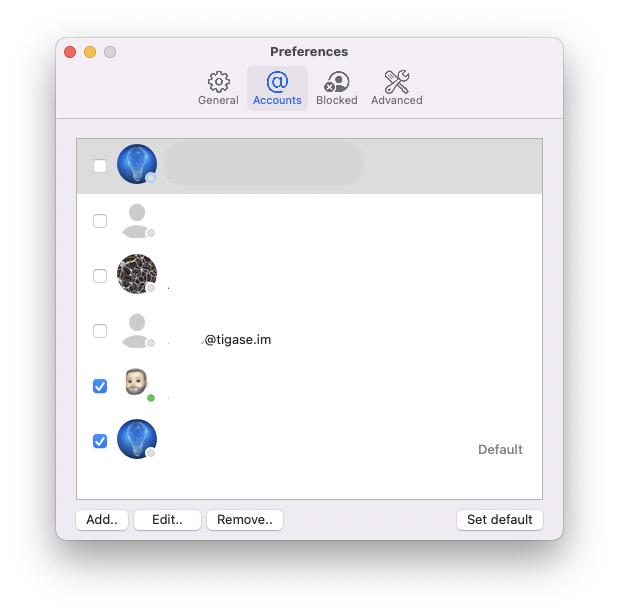
In this section, you can create an account if you don’t already have one; by clicking on the Add button, a window will appear in which you must enter the information for creating the account.
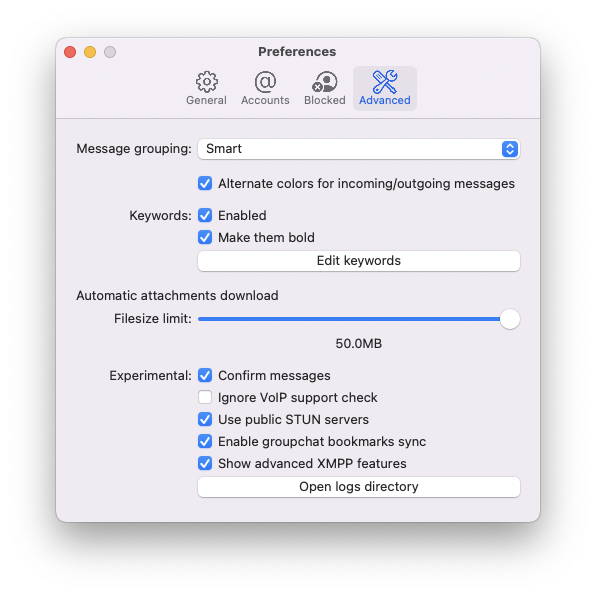
And the advanced ones
For iOS
Regarding iOS, the best apps, in our opinion, are :
Let’s clarify that Snikket is a relatively new project, and the app is nearing completion but is based on Siskin IM by Tigase.
With the new version, 7.0.1 Siskin IM is significantly improved and more stable.
Privacy
We mentioned at the beginning that XMPP is an open standard protocol.
Regarding the applications we have described, namely Beagle, Siskin IM, and Snikket, none of the developers collect personal data as indicated on the App Store.
The XMPP protocol, also through the OMEMO extension, guarantees a high level of security that prevents access to the content of messages that are encrypted on the server and always transmitted encrypted.
XMPP is a protocol whose architecture makes it similar to email and, therefore, a decentralized solution.
When creating an XMPP account, the user decides how to create the account and, therefore, which username will make up his XMPP address. Moreover, the same user chooses which nickname to use for his account, which will be the name that others will see. Finally, both for creating the account and its use no phone number is required.
If he does not want to be, the user is not identifiable.
It may detect the possible presence of user information in the username if the user provides his XMPP address to others to exchange messages.
Only the nickname is displayed if you participate in a group chat or a channel (here, the XMPP extension called MUC, the acronym for Multi-User Chat, is used).
You are the only one who decides about your account and its information and personal data.
You have control over your data and your account, deciding what information you want to change and if you wish to delete your account.
In conclusion, we have indicated a few fundamental points but, without further elaborating on the privacy aspects, it is sufficient to conduct a test by creating an XMPP account for instant messaging and using it.
You will immediately realize that you are dealing with a completely different resource from the most known and widespread ones. On the contrary, the activation of the account requires a mobile number, and those solutions are centralized (an entity controls the resource).
If this resource was helpful, you could contribute by
Or donate via
Follow us on Mastodon
Stay tuned!